Embrace Cybersecurity with Your Partners and Vendors
Top 3 Things to Know BEFORE Partnering with Vendors
As cybercrime is always knocking on the door of your business, one of the most crucial things you can do is partner with vendors that embrace a good cybersecurity posture. This means that they value your business as much as they value their own! But how do you know which vendor relationships are safe? Here are three things to know before you partner.
- Does your business have a PROCESS to audit third-party vendors for their cybersecurity resilience before sharing sensitive information?
- VERIFY that your third parties have implemented strong third-party risk cybersecurity monitoring and plans.
- DEFINE cybersecurity risk expectations and requirements with your vendors.
It’s in the Data
Payroll Companies, Financial Institutions, Accounting firms — they all have one ‘big’ thing in common. These industries store large volumes of data. Data that is very interesting to cyber criminals. It really doesn’t matter what they actual data is — just know that criminals want it!
Types of Risky Data Include:
- Employee Data
- Social Security Numbers
- Bank Account
- Health Care information
- Client Data
- Account numbers
- Sensitive information owned by Client
- Credit Card/Bank Account
- Protected Information
- Industry specific proprietary information
- Controlled Unclassified Information
As a business leader, do any of these pain points resonate with you?
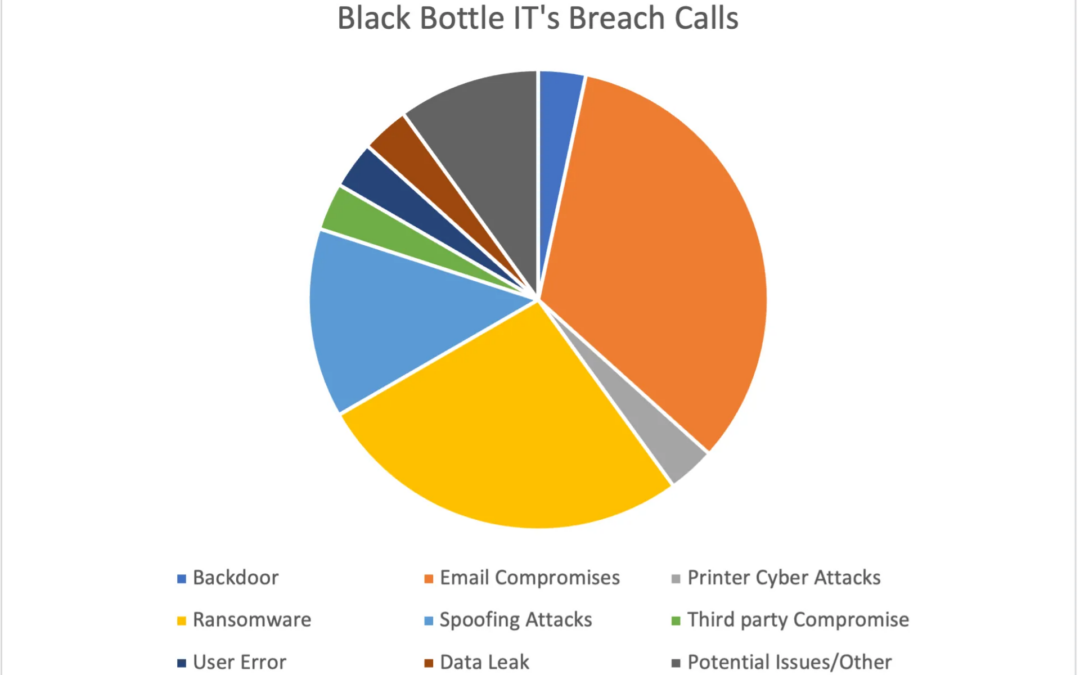
- The Increase in ransomware /phishing schemes
- Lack of compliance with increases in regulation
- Lack of an incident response plan
- Third-party vendor cybersecurity maturity
- Our Insufficient in-house cybersecurity expertise
By understanding third-party security policies and procedures, you can take corrective steps to address the risks to your data. Without the proper controls, your vendors and contractors can become the weakest link to your organization and customers’ privacy.